SharkTeam: Analysis of the KyberSwap attack
On November 23, 2023, KyberSwap was hacked on multiple networks such as Ethereum and Arbitrum due to tick manipulation and liquidity double counting, and the attackers have made a profit of about $48 million.

SharkTeam conducted a technical analysis of this incident for the first time, and summarized the security precautions, hoping that the follow-up projects can take this as a warning and jointly build a security defense line for the blockchain industry.
I. Attack Transaction Analysis
This attack is more complex and the attack implementation is more ingenious, so we select one of the attack transactions for detailed analysis and explanation.
Attack Trading:
0x09a3a12d58b0bb80e33e3fb8e282728551dc430c65d1e520fe0009ec519d75e8
Attacker address:
0x50275E0B7261559cE1644014d4b78D4AA63BE836
Attacker Contract:
0xaF2Acf3D4ab78e4c702256D214a3189A874CDC13
In this transaction, the attacker performed a series of operations against 3 different liquidity pools to drain the pools. We chose a pool for attack flow analysis, which existed independently of each other.
Attack process:
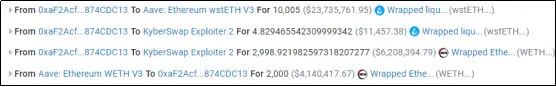
- The attacker first borrowed 10, 000 wstETH through a flash loan, then added about 2, 998 wstETH to the pool, and swapped out about 2, 842 WETH.

- At this time, the corresponding tick status in the pool is -110, 910, and the price of wstETH changes from 1.05 ETH to 0.000015257. At this time, the liquidity of the pool is 0, which paves the way for the creation of false liquidity;

- The attacker adds 3.4 wstETH liquidity and removes 0.56 wstETH in the range of [0.000014659 , 0.000015260].


- Next, the attacker makes two swaps, which are WETH->wstETH, wstETH-> WETH. After the first swap, the price was pushed down to 0.000014657, which is slightly lower than 0.000014659. After the second swap, raise the price to 0.000016368;

-
At the beginning, there was about 3 wstETH liquidity in the pool (mint 3.4 wstETH - burn 0.56 wstETH), and now there are about (1, 056 + 3, 911) in the pool, which is obviously more;
-
After the attack returns the flash loan, and the funds are transferred from the attack contract
2. Analysis of the cause of the vulnerability
The root cause of this attack: In the computeSwapStep function, there is a loss of accuracy when calculating ticks. Since the tick can be manipulated, it successfully bypasses the _updateLiquidityAndCrossTick function, allowing liquidity to be increased repeatedly.
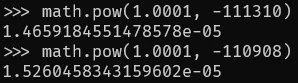
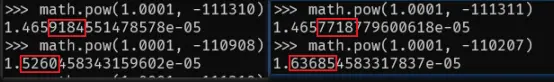
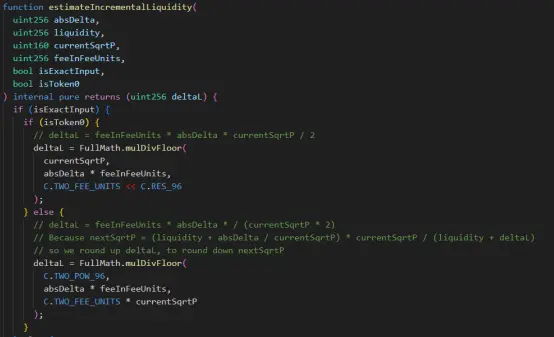
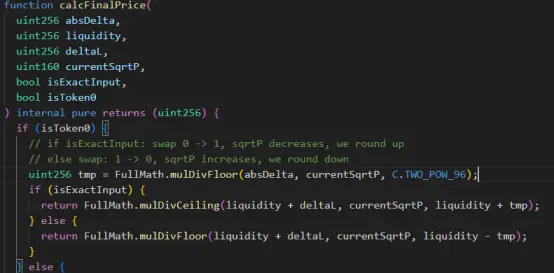
- In the first swap, the attacker uses the calcReachAmount function to calculate the amount of wstETH, and finally calculates 1, 056.056735638220800000;
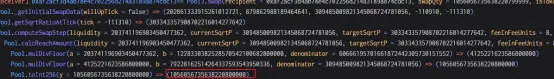
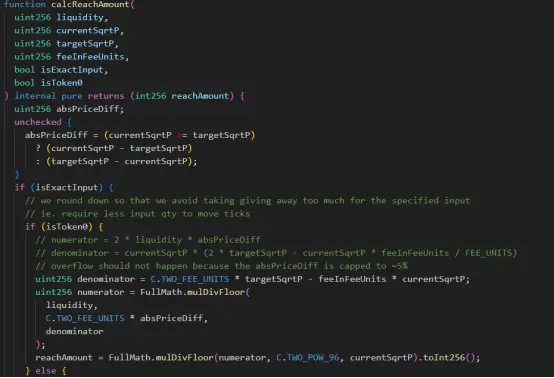
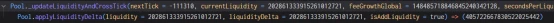
- After calling the estimateIncrementalLiquidity and calcFinalPrice functions, the number passed in is 1, 056.056735638220799999. After round up and round down, the tick is -111311 and the lower tick is -111310. Therefore, by using nextTick = currentTick+ 1 and using “!=” to judge the two sqrtP parameters, the _updateLiquidityAndCrossTick function is successfully bypassed, and the update of liquidity is avoided.
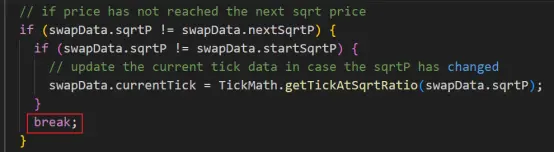
- At the second swap, _updateLiquidityAndCrossTick was called, which increased liquidity. Due to the loss of accuracy in the calculation of the quantity during the first swap, the liquidity is not updated and removed, resulting in a double situation when the liquidity is calculated on the second time.
III. Safety Recommendations
In response to this attack, developers should take the following security measures in their daily development:
-
Pay attention to the correct calculation of invariants and mathematical logic in the business to avoid loss of accuracy.
-
Before the project is released, it is necessary to cooperate with a third-party professional audit team to conduct a contract audit.
About Us
SharkTeam’s vision is to secure the Web3 world. The team is made up of experienced security professionals and senior researchers from around the world, who are well-versed in the underlying theory of blockchain and smart contracts. It provides services including on-chain big data analysis, on-chain risk warning, smart contract audit, crypto asset recovery, etc., and has created ChainAegis, an on-chain big data analysis and risk early warning platform, which supports unlimited levels of in-depth graph analysis and can effectively combat the risk of Advanced Persistent Threat (APT) in the Web3 world. It has established long-term cooperative relationships with key players in various fields of the Web3 ecosystem, such as Polkadot, Moonbeam, polygon, Sui, OKX, imToken, ChainIDE, etc.
Official Website:
Twitter:
Discord:
Telegram: