Son of a U.S. government contractor commits theft! $40 million cryptocurrency heist exposed

John Daghita is suspected of stealing over $40 million in cryptocurrency assets from a government seizure address. His father is the head of government contractor CMDSS. ZachXBT’s tracking shows a total involvement of over $90 million. CMDSS has deleted its social media accounts, and Daghita still flaunts wealth on Telegram before deleting traces. The case exposes internal access risks within government crypto custody.
Son of U.S. government contractor exploits position to steal seized assets
(Source: ZachXBT)
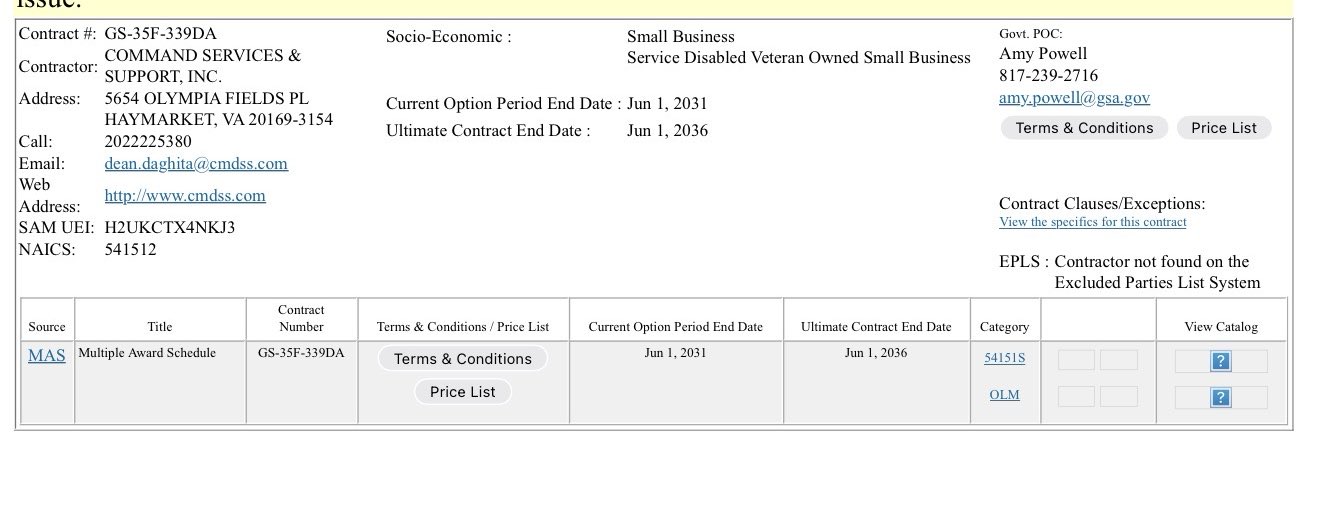
A major cryptocurrency theft scandal has erupted in the United States, alleging that John Daghita used his father’s position as a U.S. government contractor to access private crypto addresses, facilitating the theft. Daghita’s father is responsible for CMDSS, an IT company based in Virginia, which secured a contract for 2024 to assist the U.S. Marshals Service (USMS) in managing and disposing of seized and confiscated crypto assets.
This behavior of leveraging family connections to gain confidential access highlights the unique challenges governments face when handling digital assets. Traditional physical asset seizures like real estate, vehicles, or art require physical custody and transfer, making internal theft difficult. But with crypto assets, only the private keys are needed; anyone with access can transfer millions of dollars to an anonymous wallet within minutes. This digital nature significantly increases internal theft risks compared to traditional assets.
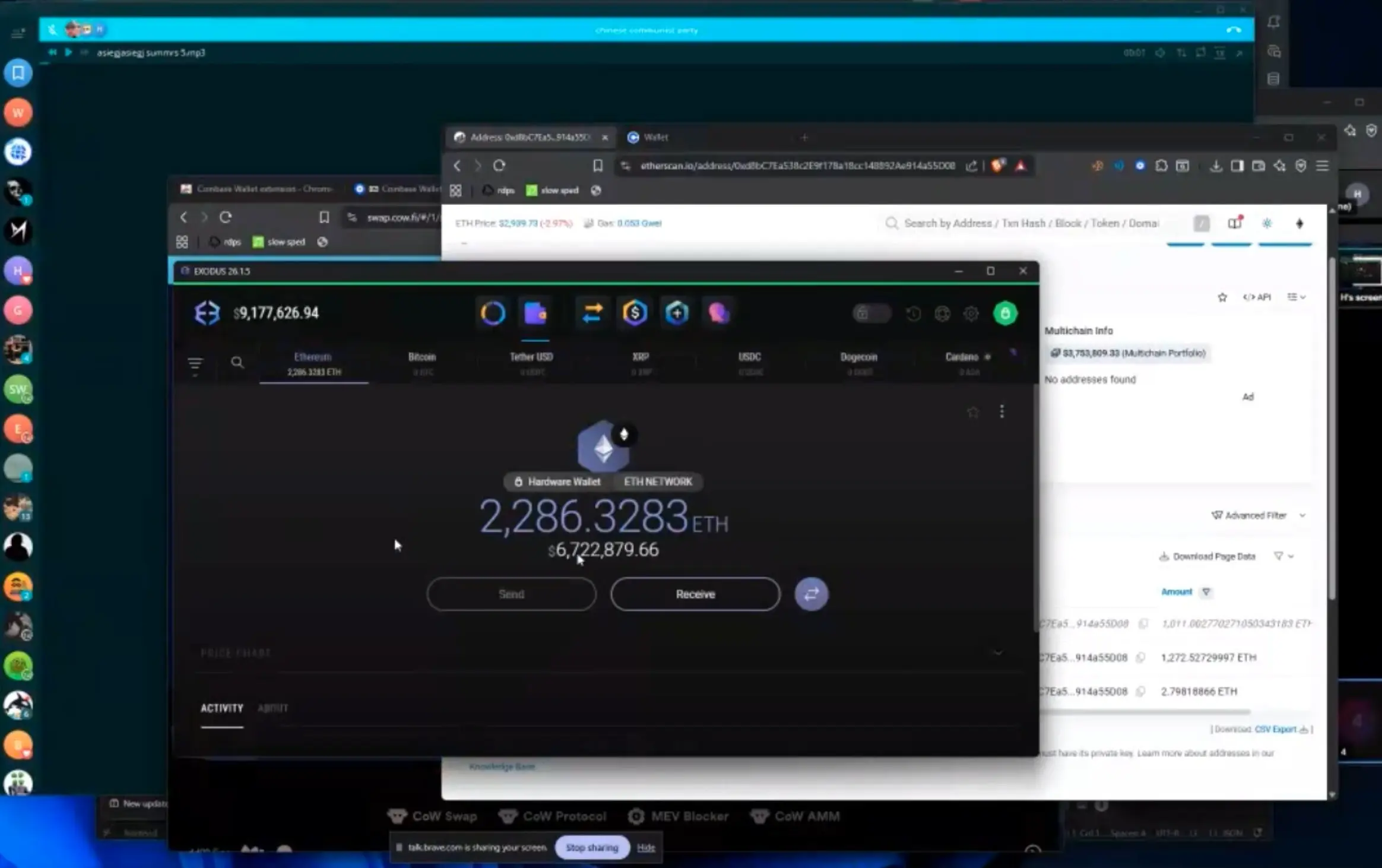
While the exact mechanism remains unclear, reports indicate that blockchain investigator ZachXBT has traced at least $23 million related to a single wallet. This wallet is directly linked to cases involving over $90 million in stolen assets, occurring between 2024 and late 2025. This suggests the theft may be just the tip of the iceberg, with actual involved amounts far exceeding the initial $40 million report.
CMDSS is not a small player in government IT contracting. Over the years, it has maintained effective contracts with the Department of Defense and the Department of Justice. This raises concerns: prior to the scandal, how much sensitive information or assets might Daghita have accessed? Given the company’s long-term engagement in sensitive government projects, its employees and their families should theoretically undergo strict background checks and security clearances. But this crypto theft case reveals vulnerabilities in these security measures when facing insider threats.
CMDSS takes emergency action to erase traces; suspect flaunts wealth on Telegram
(Source: ZachXBT)
In response to the escalating scandal, CMDSS deleted its X (Twitter) and LinkedIn accounts and cleared employee and team information from its website. This “digital self-immolation” crisis response is extremely rare; usually, such drastic measures are only taken in the face of severe legal or reputational crises. While deleting all digital footprints can temporarily prevent public digging, in an era where blockchain and internet archives are permanent, this approach has limited effectiveness.
Even more shocking, ZachXBT pointed out that Daghita remains active on Telegram, flaunting assets related to the theft and even interacting with public addresses involved in the investigation. Such blatant provocation is rare in crypto theft cases; most thieves immediately cut all digital ties and attempt to hide their identities. Daghita’s behavior may be motivated by overconfidence, lack of understanding of blockchain tracking, or believing he has some form of protection.
Reports indicate that after posting, Daghita quickly deleted NFT usernames from his Telegram account and changed his display name, further complicating efforts to trace stolen funds. However, these post-hoc measures are of limited significance to blockchain investigators, as Telegram messages and interactions may have been screenshot, and blockchain transactions are immutable. Daghita’s actions might even serve as evidence of “realizing the crime.”
Timeline and key actions in this case
2024: CMDSS secures U.S. Marshals crypto asset management contract
2024-2025: Multiple cases involving over $90 million in suspected theft occur
ZachXBT tracking: At least $23 million linked to a single wallet
After scandal exposure: CMDSS deletes all social media accounts and employee info
Daghita’s response: Flaunting wealth on Telegram, then deleting NFT usernames and changing name
Systemic vulnerabilities in government crypto custody exposed
This crypto theft highlights serious flaws in government contracting and internal risk management. The case reveals internal access risks within government crypto custody and contractor oversight. Even with robust regulations, interpersonal relationships and internal personnel involvement pose significant risks. This incident underscores recurring vulnerabilities in crypto custody arrangements, even within government-approved frameworks.
Investigators continue to examine the technical and organizational aspects of this suspected theft. Reports indicate authorities are reviewing CMDSS’s operational procedures and the extent to which the company’s contracts with the government may have inadvertently facilitated access to high-value crypto assets. Key questions include: Does CMDSS have proper multi-signature controls? How are private keys stored? Who has access rights? Are there audit logs tracking all access?
Analysts urge immediate audits and increased transparency to assess the full scope of potential losses. The John Daghita theft is one of the most prominent recent cases of U.S. government contractor-related crypto asset leaks. This incident may prompt the U.S. government to reevaluate its crypto custody policies, including whether to fully outsource custody to private contractors or establish stricter multi-signature and audit mechanisms.
For the crypto industry, this case offers a vital lesson: even government-level custody arrangements cannot fully eliminate insider risks. Multi-signature setups, hardware security modules, regular audits, and least-privilege access principles are fundamental to protecting large crypto holdings. Any custody arrangement where a single individual or entity has complete control carries the risk of misuse.