The U.S. Department of the Treasury expands cyber security intelligence, and encrypted companies receive traditional finance–level protection

The U.S. Department of the Treasury’s Office of Cybersecurity and Critical Infrastructure Protection (OCCIP) announced Thursday that it is expanding the coverage of its cyber threat identification program to digital asset companies. Blockchain firms that choose to join will “receive” the same level of cyber threat intelligence as traditional financial institutions for free. In 2026 Q1, cumulative losses from hacker attacks suffered by decentralized finance (DeFi) platforms are approaching $169 million.
OCCIP Program Breakdown: Blockchain Companies Can Get Threat Intel for Free
The core of this expansion is bringing the cryptocurrency industry into the cyber threat identification framework that previously covered only traditional financial institutions. According to the Treasury Department’s announcement, participating blockchain companies will receive threat intelligence services at the same level as traditional financial institutions such as banks and securities firms—and at no cost.
The background to this policy is that the cryptocurrency industry has long operated outside regulatory frameworks and lacks systematic government threat intelligence support. As a result, when facing attacks from foreign intelligence agencies and organized crime groups, it often has to rely only on its own security resources. This move by the Treasury Department marks a shift in how the U.S. government categorizes cybersecurity for the digital asset industry—from peripheral financial activities to critical financial infrastructure that requires systematic protection.
Threats Escalate: Drift Protocol Reveals North Korea’s Full Playbook for Infiltrating Crypto
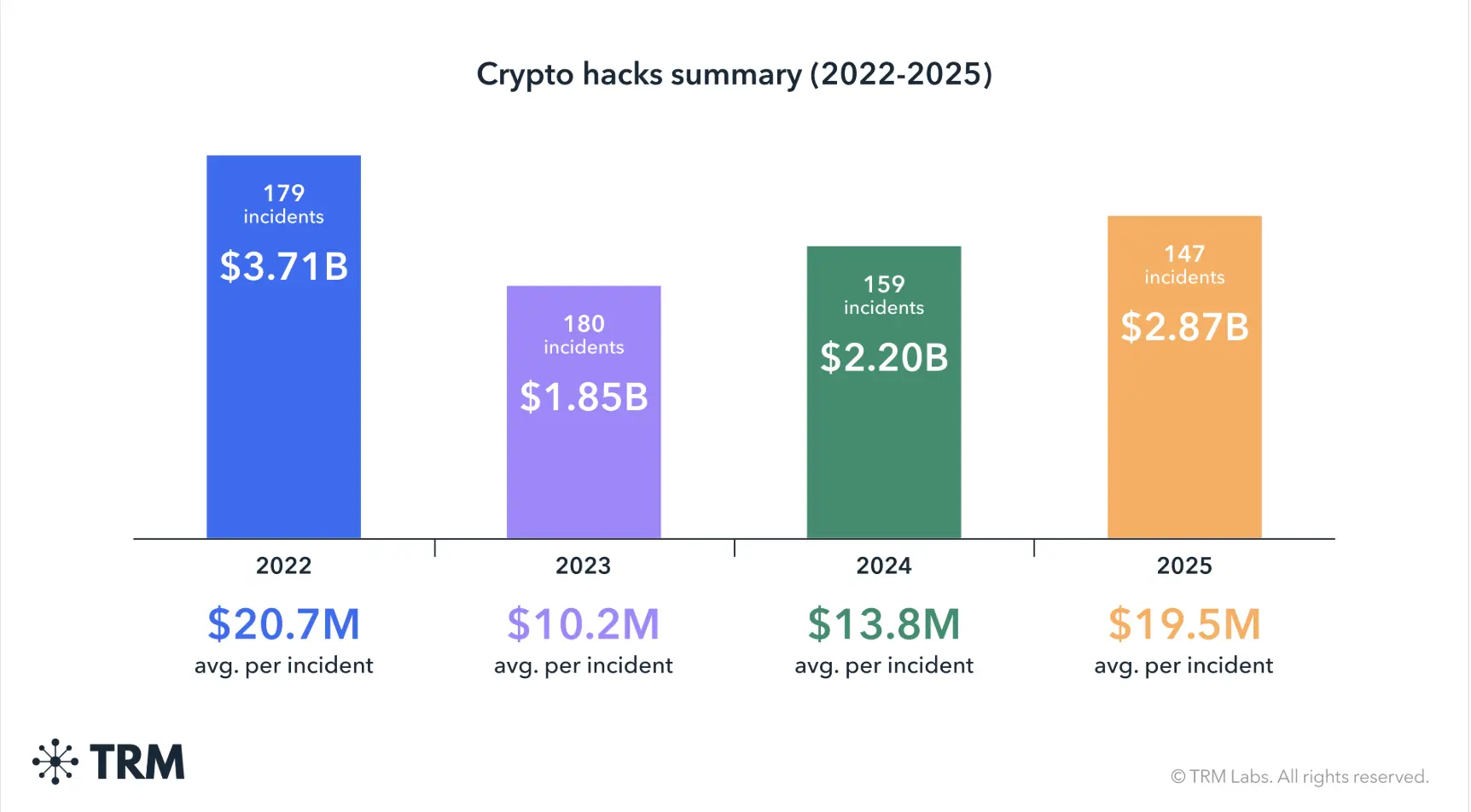 (Source: TRM Labs)
(Source: TRM Labs)
The urgency of the Treasury Department’s expanded protection program is made clear by a series of recent major attack incidents. This month, the decentralized exchange Drift Protocol suffered an attack totaling $280 million, and the attackers are believed to be connected to North Korea.
North Korea’s Infiltration Pattern Exposed by the Drift Protocol Attack
Social engineering intrusion: The attackers initially made in-person contact with the Drift team at a large cryptocurrency industry conference, establishing a “reasonable” initial relationship.
Long-term infiltration: In the months after the first meeting, the attackers continued interacting with the Drift team, gradually building trust.
Malware implantation: After months of relationship maintenance, the attackers successfully deployed malware designed to steal cryptocurrency on the machines of Drift developers.
Scheduled activation of the attack: The malware was activated during an April vulnerability incident, leading to $280 million in losses.
Man-in-the-middle cover: Reports indicate that the person who initially reached out to the Drift team was not a North Korean national, suggesting the attackers used a third-party intermediary as a cover.
Seals911, a blockchain network cybersecurity expert team, said they have a “moderate-to-high level of confidence” that this attack is linked to the October 2024 Radiant Capital hacker incident as part of the same organization. The North Korea-linked Lazarus Group is believed to be associated with multiple similar attacks.
Policy Background: Closing the Long-Standing Security Gap in the Crypto Industry
The policy basis for the Treasury Department’s action comes from the report issued by the Trump administration in July 2025, titled “Strengthening U.S. Leadership in the Digital Financial Technology Sector.” The report explicitly lays out the policy direction of including digital asset companies within the federal cybersecurity protection framework.
In terms of threat scale, TRM Labs’ data shows that cumulative losses from cryptocurrency hacker attacks between 2022 and 2025 have been enormous. And the $169 million DeFi loss in 2026 Q1 shows that attack frequency and scale have not declined despite regulatory pressure. The rollout of this Treasury Department plan represents a systematic action by the U.S. on cybersecurity policy for crypto networks, not merely a temporary measure in response to a single incident.
Frequently Asked Questions
What specific protections does the U.S. Treasury’s cyber threat intelligence program provide to crypto companies?
According to the Treasury Department’s announcement, blockchain companies that join the program will receive cyber threat intelligence at the same level as traditional banks and securities firms for free, including real-time threat identification, analysis of attack methods, and risk alerts. This helps crypto companies identify and prevent cyberattacks targeting their platforms in advance.
How does North Korea’s Lazarus Group attack cryptocurrency companies?
Based on the pattern revealed in the Drift Protocol attack incident, North Korea-linked groups typically use long-term social engineering tactics: first, establish contact relationships at industry events, then build trust through months of interaction, and finally implant malware on the target developers’ devices, waiting for the right moment to trigger it. This approach is far more covert than direct technical exploitation of vulnerabilities.
Does this Treasury Department action mean the crypto industry is officially being included in the protection framework for critical financial infrastructure?
The rollout of this expanded program signifies that the U.S. government, at the policy level, is bringing the digital asset industry within the scope of financial infrastructure that needs systematic protection. The policy recommendations from the Trump administration’s July 2025 report have been implemented in practice, showing that the U.S. is proactively closing the institutional gap left by the long-term lack of federal cybersecurity support for the crypto industry.