Drift Hacker Case: How a North Korean Hacker Infiltrated for 6 Months and Planned the Largest DeFi Heist of Spring 2026
Drift suffered North Korea-linked infiltration for more than half a year, using social engineering and Durable Nonce to steal roughly $280 million in assets, severely damaging DeFi’s security and trust.
A meticulously planned operation spanning half a year: from meeting small talk to a $280 million heist
On April 1, instead of April Fools’ Day filled with pranks, Drift Protocol—the leading sustainable derivatives trading exchange in the Solana ecosystem—was hit by a catastrophic real-world blow. Within just 10 seconds, this attack caused approximately $280 million to $286 million in users’ assets to vanish out of thin air, setting a record for the largest hacker incident in the DeFi industry since 2026.
- Related news: DeFi platform Drift was hacked on April Fools’ Day! The hacker emptied $270 million in assets; the admin’s private key was the vulnerability
According to the post-incident investigation report released by the Drift team, this incident stemmed from a “structured intelligence operation” that had been brewing for over 6 months and had a state-level organizational background. Initial findings indicate the operation is highly connected to the North Korea threat organization UNC4736 (also known as AppleJeus or Citrine Sleet), which previously carried out a $50 million attack on Radiant Capital in October 2024. This penetration operation targeting Drift skipped traditional code-vulnerability research and instead relied on extremely high-precision human manipulation, bypassing multiple layers of protection including code audits and hardware wallets.
Image source: X/@DriftProtocol Drift team’s post-incident investigation report; the incident originated from a “structured intelligence operation” that had been brewing for over 6 months and had a state-level organizational background
North Korea hackers’ “shadow proxy” strategy
This long-game scam began with a large cryptocurrency conference in October 2025. At the time, several individuals who claimed to be representatives from quant trading firms proactively reached out to Drift’s core team members and expressed interest in collaborating on protocol integration and liquidity provision.
Over the following six months, these hackers demonstrated exceptionally high professional conduct and technical competence. They frequently discussed trading strategies with the development team through Telegram channels. Even between December 2025 and January 2026, they actually deployed a fully featured “Ecosystem Vault” on Drift and deposited more than $1 million of their own funds to establish credit.
Notably, the individuals who appeared in person at the conference to validate Drift were not North Korean. This suggests North Korea hackers have been frequently hiring third-party intermediary organizations or deploying agents with near-perfect identities to carry out real-world social engineering. This “deep cultivation” approach helped the Drift team lower its guard and treat the lurking threat as long-term reliable business partners.
Durable Nonce and vulnerabilities in development tools
After building deep trust, the hackers began executing their final intrusion plan by infecting developers’ work devices through sharing malicious code repositories (Repos) or inviting them to install a testing version app (TestFlight). The investigation indicates that the attackers exploited serious security vulnerabilities present in the development tools VSCode and Cursor at the time. Developers only needed to open a specific folder in the editor, and the malicious code would automatically run without any prompts.
Once they successfully gained control of the devices of two Security Council members, the hackers induced them to sign authorization instructions that granted management privileges. After that, they leveraged Solana’s legitimate feature called “Durable Nonces” to store these pre-signed transaction instructions on the blockchain for as long as a week to evade detection.
Until April 1, the trap was fully sprung, and the hackers executed 31 withdrawal transactions in 10 seconds. The affected assets were highly widespread, including the $JLP token worth $155 million, as well as more than $66.4 million in $USDC, $477k in $WETH, and other major assets, causing Drift’s total value locked (TVL) to plunge from $550 million to less than $250 million. The price of its native token DRIFT also fell by more than 98%.
Civil negligence dispute and AI threats—forced transition as a security benchmark for DeFi
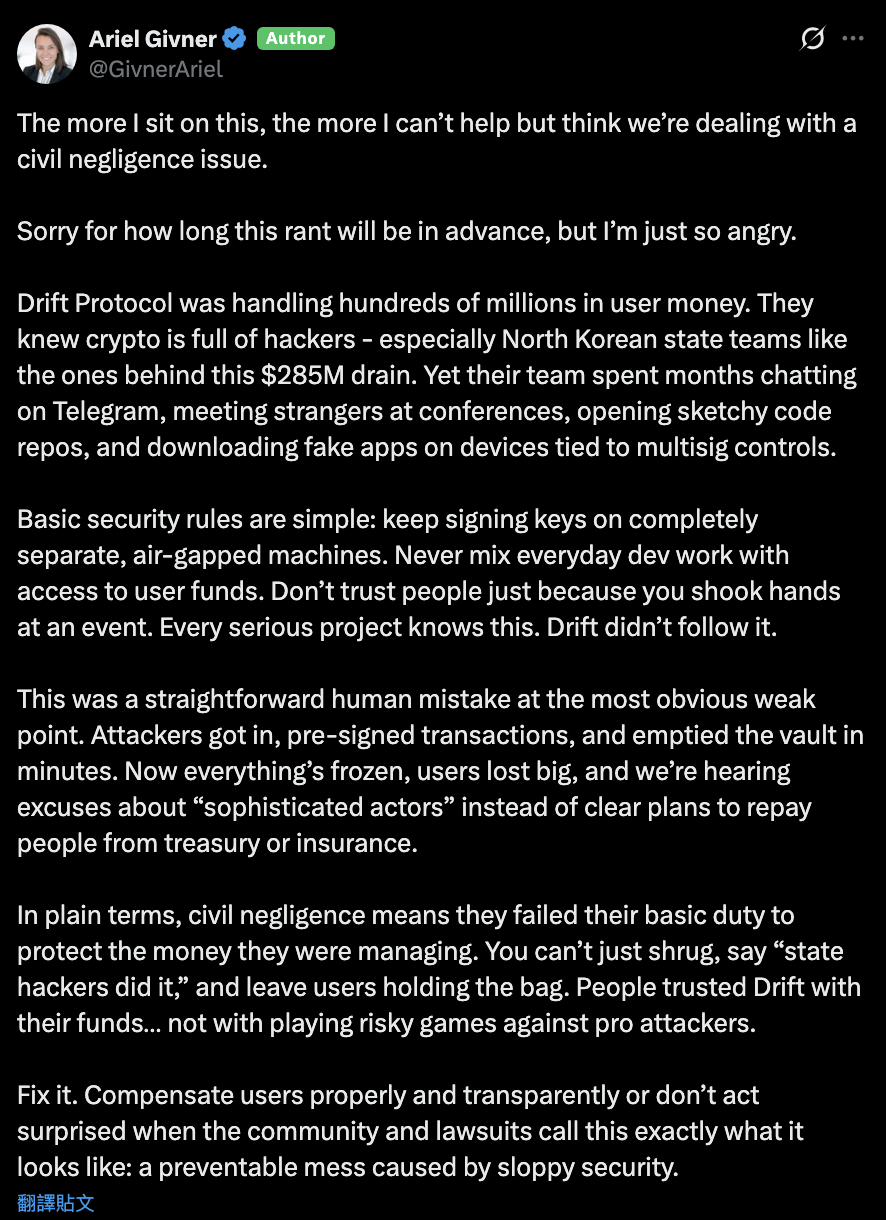
The incident sparked strong criticism from both the legal and technical communities. Crypto attorney Ariel Givner noted that the Drift team’s actions could constitute “civil negligence,” because the development team failed to follow basic operational security practices, such as storing signing keys on fully isolated physical devices (air-gapped systems), and opening external files of unknown origin on devices linked to permission management.
Image source: X/@GivnerAriel Crypto attorney Ariel Givner said the Drift team’s actions could constitute “civil negligence”
At the same time, Ledger CTO Charles Guillemet warned that, with the development and widespread adoption of AI technology, the cost of carrying out this kind of sophisticated social engineering is trending toward zero. AI can generate highly persuasive fake identities and technical documents, making the human defense line increasingly fragile. Currently, Drift has frozen all protocol functions and is attempting to conduct on-chain negotiations with the hackers’ wallets, but the broader community remains largely pessimistic about the chances of recovering funds.
This heist delivers a harsh warning to the entire industry: when hackers have shifted to attacking human psychology rather than code logic, relying solely on multisig wallet governance can no longer guarantee asset safety. Strengthening operational discipline and enforcing hardware isolation is the only viable way to defend against state-level threats.
Further reading
Drift hacked—whose fault? Cross-chain assets weren’t frozen; ZachXBT slams Circle for negligence