What Is Q-Day: Quantum Computing Fundamentals, Cryptographic Implications, and Cryptocurrency Risk Transmission
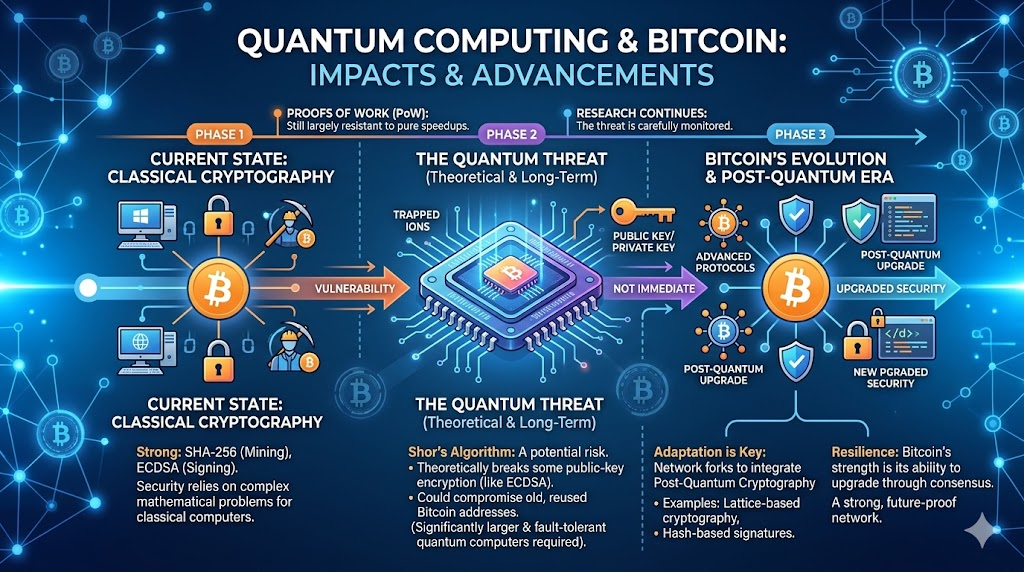
In discussions about financial security and distributed ledgers, "Q‑Day" typically refers to the point at which quantum computing becomes a real, practical threat to widely implemented asymmetric cryptography—not an instantaneous entire network event. Both industry and academic sources provide baseline, optimistic, and pessimistic projections, with differences mainly arising from assumptions about logical qubit scale, gate operation resources, physical error rates, and algorithmic constants.
Definition and Boundaries
Public conversation often conflates Q‑Day with "quantum supremacy" or "quantum advantage," but in cryptographic contexts, the focus is on CRQC: demonstrating not just specialized sampling tasks, but scalable attack pathways against structures like RSA, finite fields, or elliptic curve discrete logarithms within defined cost and time constraints. Three common boundaries emerge:
- Time: Most indicators are intervals or sensitivity analyses—rarely a single calendar date.
- Target: Threats are aimed at the combination of cryptographic primitives, parameter choices, and system implementations, not simply a linear "quantum computers automatically migrating on-chain Assets" storyline.
- Information: Many models require a clearly defined attack surface—such as the difference between on-chain, publicly exposed Public Key material and commitments that only reveal Hashes, each with distinct exploitability.
Quantum Computing: Fundamental Concepts
Qubits leverage superposition to encode richer information structures within Hilbert space; entanglement means that multi-particle states cannot be decomposed into separate individual states, forming the basis for many quantum algorithms. Real-world quantum processors are limited by noise and decoherence, necessitating quantum error correction to approach the long-term reliability of fault-tolerant quantum computing. Engineering discussions therefore focus on metrics like logical qubit equivalence, fault tolerance thresholds, error correction overhead, gate fidelity, and calibration cycles.
Quantum algorithms can offer super-polynomial resource advantages over classical computing for certain problem types. Shor’s algorithm is a prime example, directly undermining the public key hardness assumptions based on specific algebraic structures.
Shor’s Algorithm and Cryptocurrencies’ Curves
Shor’s algorithm, introduced in 1994, enables polynomial-time solutions for integer factorization and discrete logarithm problems in quantum systems. Mainstream blockchain addresses and Signature rely on the hardness of elliptic curve discrete logarithms—for example, Bitcoin uses Signature tied to secp256k1 (historically ECDSA, later including Schnorr schemes).
In threat modeling, on-chain data containing Public Keys or reconstructable Public Keys—when combined with sufficiently powerful fault-tolerant quantum computation—turns the classic "Private Keys can’t be derived from public information" assumption into a risk assessment: focus shifts to the transition period, timing of key exposure, and whether migration introduces new interactive requirements.
Structural Factors in Cryptocurrency Ecosystems
Open ledgers impose three constraints distinct from Web PKI:
- Historical transparency: Past Trade(s) can be replayed indefinitely, potentially feeding future algorithms.
- Consensus upgrade paths: Cryptographic migration relies on network rule changes and widespread client adoption, which are slow and involve complex game theory.
- Economic and incentive alignment: Miners/Validator, Wallet Developer, businesses, and users may not share priorities or timelines.
On-chain post-quantum migration options include hybrid Signature, ZK (zero-knowledge) proofs, or new opcodes supporting post-quantum Signature verification. When comparing these, key metrics include gate count, logical qubit scale, error rate projections, on-chain interaction costs, and compatibility—not just conceptual slogans.
In Plain Terms: How Quantum Computing Could Change Blockchain
Think of a blockchain Wallet as a "public address and private key." Normally, knowing someone’s address isn’t enough—Private Keys are extremely hard to reverse-engineer. With advanced quantum computing, the difficulty of breaking some traditional Signature algorithms could drop sharply, letting attackers forge Signature much faster. For blockchains, the real issue isn’t just "can the technology be broken," but "how long will it take the entire network to upgrade": protocols, Wallets, exchanges, and Custodian all need to migrate to post-quantum solutions. The slower the transition, the longer the period of risk for Assets whose Public Keys have already been exposed.
How to Read 2026 Public Information and Research
Project Eleven’s 2026 roadmap release, The Quantum Threat to Blockchains 2026, sets the Q‑Day baseline around 2033, with optimistic and pessimistic scenarios (commonly cited as 2030 and 2042; always check original sources for specifics). The release argues that blockchains with widespread elliptic curve Signature will need a multi-layer redesign, and this discussion should be iterative: new hardware benchmarks and research can prompt timely scenario updates rather than fixating on a single date.
Publications on platforms like Cryptology ePrint Archive regularly offer updated resource estimates for elliptic curve threat models. Conclusions depend on model parameters, so readers must check target bit-lengths, fault tolerance methods, parallel strategies, and constant factors for alignment with the target chain.
Ecosystem Response Strategies
Typical technical responses include pilot deployments of NIST post-quantum algorithms in enterprise settings, shortening certificate and key lifespans, and tracking technical proposals for specific chain migrations. For end users, key verification points include:
- Whether the target network has published a PQ (post-quantum) migration roadmap and compatibility plan;
- Whether Wallet implementations stay synced with consensus-layer and security updates;
- Whether key rotation and algorithm upgrade policies in custodial or multi-signature processes are auditable.
Cryptography risks and secondary market volatility belong to different evaluation frameworks; this article focuses only on conceptual structures and types of information.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


